131 Spamware Extensions Targeting WhatsApp Flood Chrome Web Store
The Socket Threat Research Team uncovered a coordinated campaign that floods the Chrome Web Store with 131 rebranded clones of a WhatsApp Web automation extension to spam Brazilian users.
This cluster of Chrome extensions comprises 131 rebrands of a single tool, all sharing the same codebase, design patterns, and infrastructure. They are not classic malware, but they function as high-risk spam automation that abuses platform rules.
The code injects directly into the WhatsApp Web page, running alongside WhatsApp’s own scripts, automates bulk outreach and scheduling in ways that aim to bypass WhatsApp anti-spam enforcement. Listings and marketing sites claim that their Chrome Web Store presence implies a rigorous audit and full privacy compliance. That claim is inaccurate and conflicts with Chrome and WhatsApp policies. At the supply chain level, this is policy abuse that enables spam at scale. Across listings with visible counts, these extensions account for at least 20,905 active users.
All 131 extensions were live in the Chrome Web Store at the time of writing. We have filed takedown requests with the Chrome security team and requested suspension of the related publisher accounts for policy violating spamware.
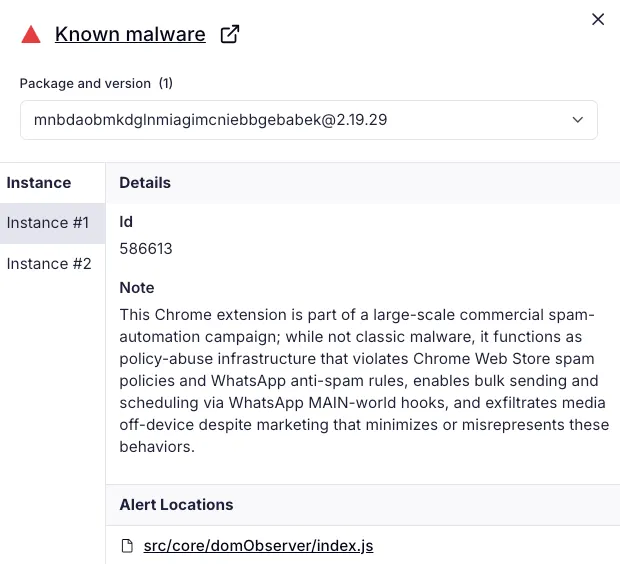 Socket AI Scanner flags the Chrome extension mnbdaobmkdglnmiagimcniebbgebabek (Organize-C) as malware due to spamware behavior: it injects code into the WhatsApp Web page to automate bulk messaging and scheduling, violates Chrome Web Store and WhatsApp policies.
Socket AI Scanner flags the Chrome extension mnbdaobmkdglnmiagimcniebbgebabek (Organize-C) as malware due to spamware behavior: it injects code into the WhatsApp Web page to automate bulk messaging and scheduling, violates Chrome Web Store and WhatsApp policies.
Gaming the Store
Based on Chrome Web Store timestamps and our captures of the 131 unique listings (see IOCs), the operation has run for at least nine months. Rebrands and updates landed in regular waves throughout 2025, with new uploads and version bumps observed as recently as October 14, 2025.
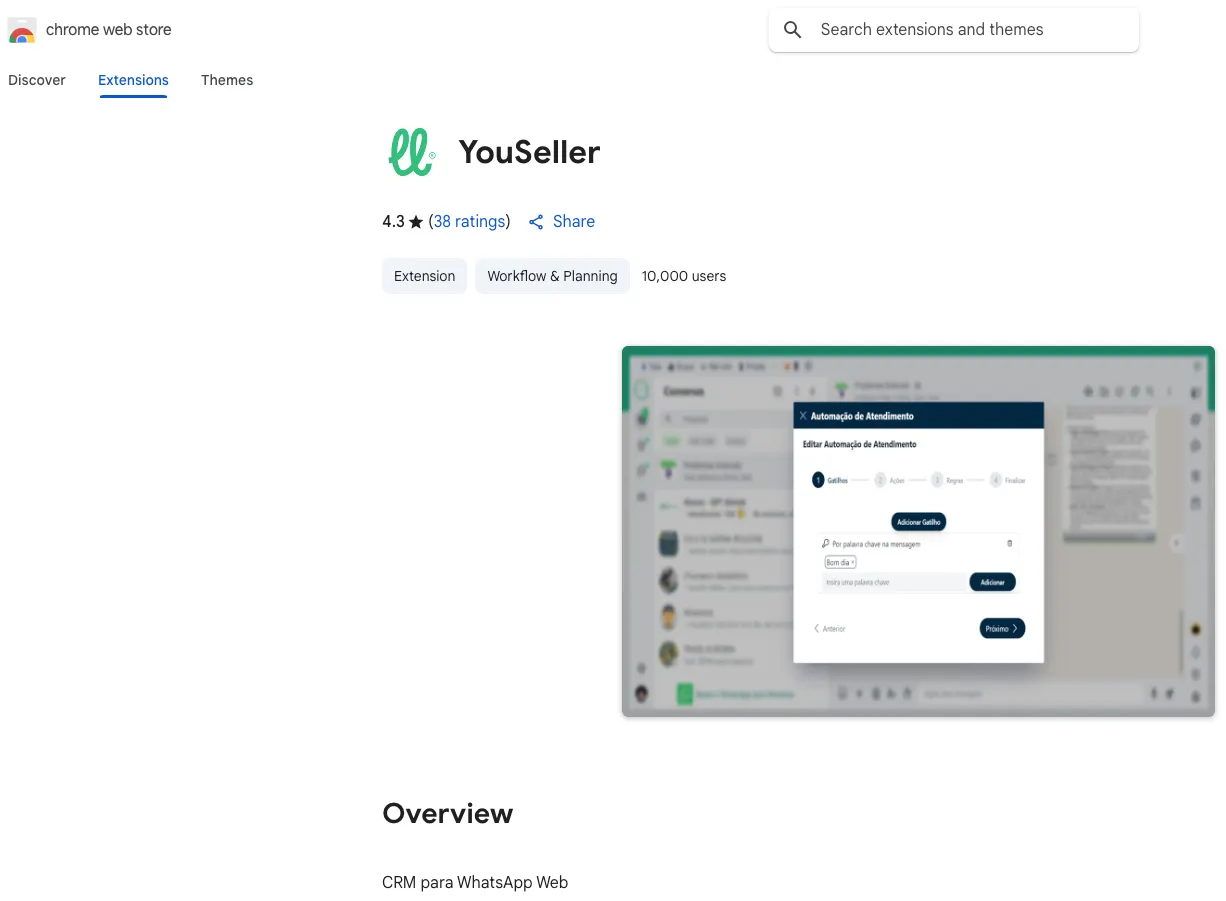
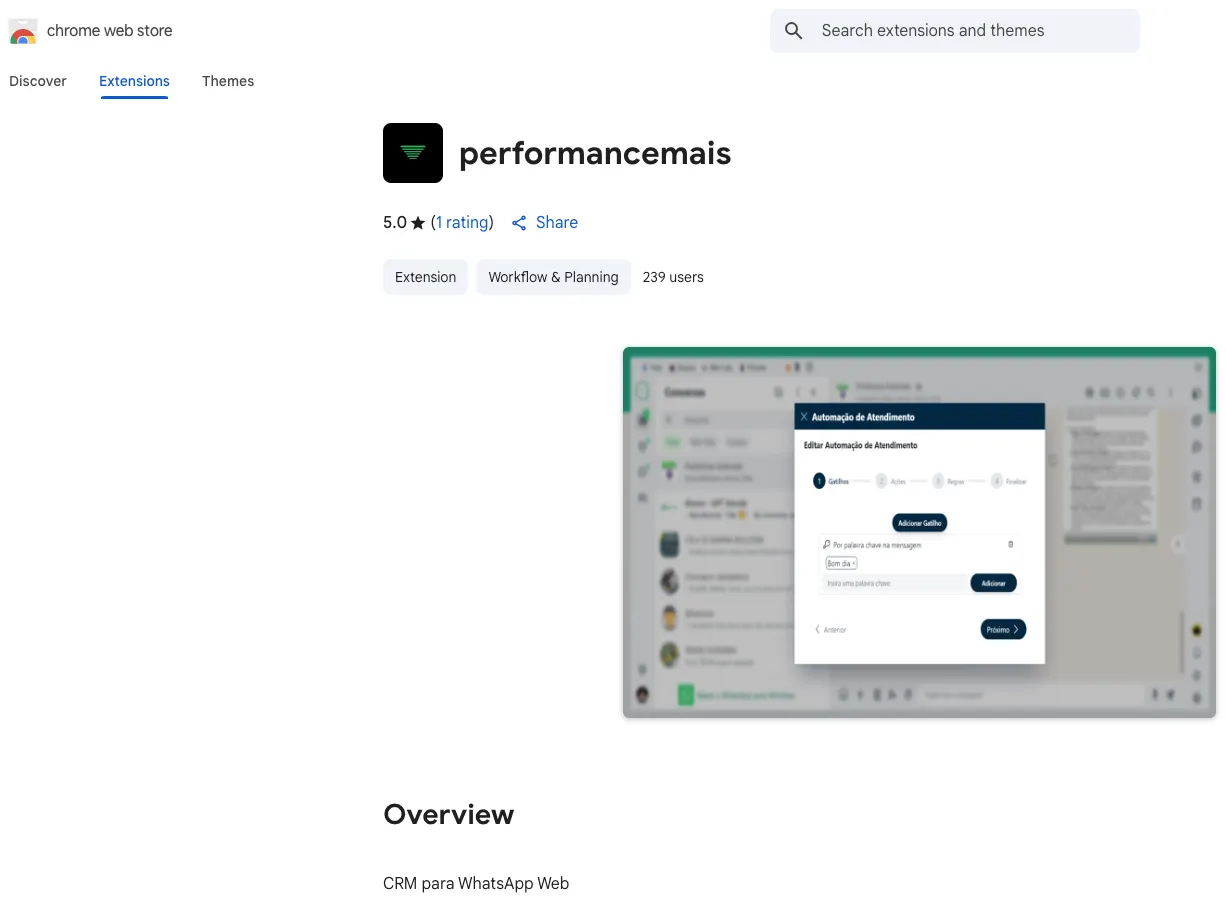
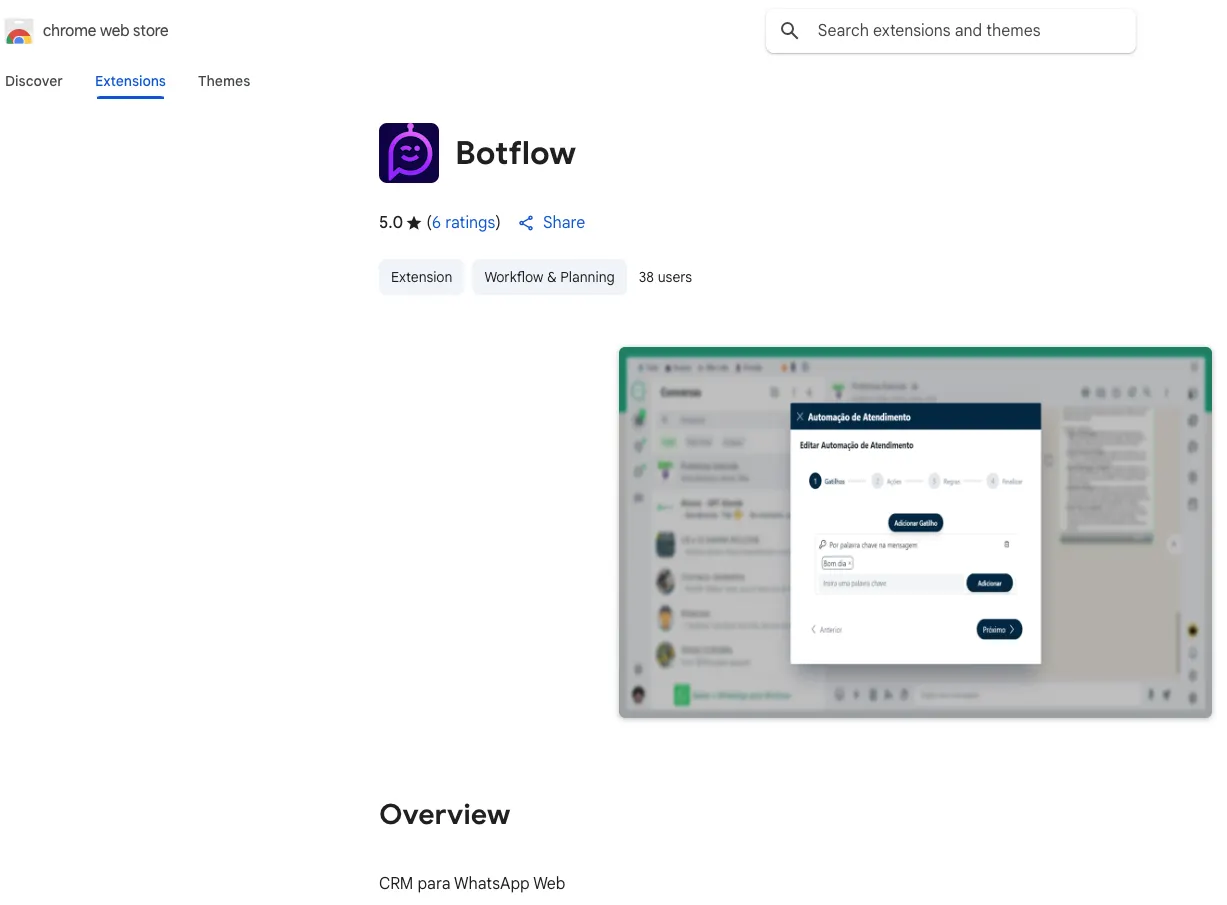
Chrome Web Store listings, top to bottom:
YouSeller(10,000 users),performancemais(239 users), andBotflow(38 users). Each shows the same WhatsApp Web automation interface, consistent with a spamware clone cluster that reuses design, imagery, descriptions, and codebase. Note: the “users” metric reflects active users, not total installs.
Extensions use different names, logos, and glossy landing pages, but the code and infrastructure are the same. The dominant publisher label is WL Extensão and its variant WLExtensao, which appears on 83 listings. Despite the varied branding, the entire cluster was published through only two developer accounts: suporte@grupoopt.com[.]br and kaio.feitosa@grupoopt.com[.]br. The features look business facing, but the operational goal is aggressive outbound messaging that aims to evade WhatsApp rate limits and anti-spam controls.
Marketing Strategy
It is akin to a franchise model: the operator and affiliated sellers publish dozens of near identical copies under new names and logos, then promote them with lookalike sites that sell monthly plans and pitch investment benefits in Portuguese to Brazilian small businesses. Many of these sites claim that Chrome Web Store inclusion means a rigorous audit and code review that guarantees privacy and safety. Chrome’s process is a policy compliance review, not a certification, and presenting it as an audit misleads buyers and creates a false sense of security.
For clarity, screenshots in this post include translations from Portuguese to English.
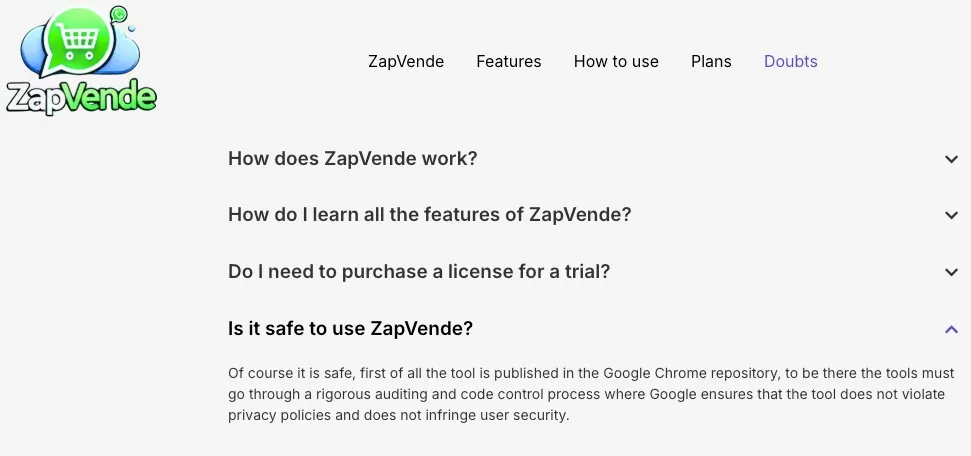 ZapVende, one of the extensions in this cluster, is marketed at zapvende[.]com, which asserts the extension is safe simply because it is listed in the Chrome Web Store.
ZapVende, one of the extensions in this cluster, is marketed at zapvende[.]com, which asserts the extension is safe simply because it is listed in the Chrome Web Store.
DBX Tecnologia (DBX Technology Group), the operator of the original extension that spawned 131 clones, markets a reseller program. DBX Tecnologia and Grupo OPT, which operates the grupoopt.com[.]br domain, are effectively two arms of the same business under the same founder, not unrelated companies. Both describe their work as an ecosystem that builds WhatsApp-based solutions, among other products.
 DBX Tecnologia reseller white-label program: invest R$12,000 (~USD $2,180) to rebrand and sell its WhatsApp Web extension under your own name, with promised 30 to 70 percent margins and R$30,000 to R$84,000 (~USD $5,450 to ~USD $15,270) in recurring revenue, illustrating the “franchise model” behind the 131 clone flood.
DBX Tecnologia reseller white-label program: invest R$12,000 (~USD $2,180) to rebrand and sell its WhatsApp Web extension under your own name, with promised 30 to 70 percent margins and R$30,000 to R$84,000 (~USD $5,450 to ~USD $15,270) in recurring revenue, illustrating the “franchise model” behind the 131 clone flood.
Based on the DBX Tecnologia YouTube pitch, a “white-label partnership” means that:
- DBX supplies the product, the partner supplies the brand. The partner pays an upfront fee to license the WhatsApp Web automation extension, DBX swaps in the partner’s logo, name, some design features, and provides marketing assets and tutorials.
- The partner publishes and sells it as if it were their own tool.
- DBX maintains the core code and backend. The partner’s branded build still communicates with DBX-controlled services when features are used, and receives updates from the same codebase.
- Revenue flows to the partner minus DBX program fees or revenue share. DBX advertises high margins and recurring income because partners resell subscriptions to end customers.
Practical caveats: if listed as a publisher, the partner carries policy and reputational risk. Bulk messaging with spam scheduling collide with WhatsApp’s opt-in rules and Chrome Web Store spam and duplication policies, so partners and their customers face takedowns and account bans. If features route media to vendor infrastructure, the partner must disclose that data flow and provide a privacy policy.
Distribution Infrastructure
Lobo Vendedor is marketed at lobovendedor[.]com[.]br, one of at least 23 near-identical sites we found that promote individually branded clones of the same extension. Many of the extensions are also backed by matching YouTube, LinkedIn, Instagram, and TikTok accounts that funnel buyers into subscriptions.
The pitch centers on aggressive outreach at scale on WhatsApp, with automation, templates, and scheduling that maximize reach. This reseller strategy multiplies distribution, and it steers customers toward conduct that violates Chrome Web Store rules on duplicate and spammy extensions and WhatsApp’s requirement for recipient opt-in. The impact lands on ordinary users, who receive unsolicited promotional messages at volume, and the burden of defense shifts to recipients who must block numbers and report abuse after the fact.
 Lobo Vendedor marketing page (lobovendedor[.]com[.]br) promotes a rebranded clone of the WhatsApp Web automation extension, resold to agencies and SMBs for bulk outreach. The site illustrates the reseller model driving this clone cluster and pushes mass messaging that conflicts with WhatsApp’s opt-in rules.
Lobo Vendedor marketing page (lobovendedor[.]com[.]br) promotes a rebranded clone of the WhatsApp Web automation extension, resold to agencies and SMBs for bulk outreach. The site illustrates the reseller model driving this clone cluster and pushes mass messaging that conflicts with WhatsApp’s opt-in rules.
Chrome Web Store Policy in Context
Google’s Chrome Web Store Spam and Abuse policy bans developers and their affiliates from submitting multiple extensions that provide duplicate experiences. It also prohibits manipulating placement through ratings or installs, blocks extensions that send spam or unwanted messages, and forbids sending messages on a user’s behalf without giving the user a chance to confirm the content and recipients. These rules map directly to our findings: the cluster consists of near identical copies spread across publisher accounts, is marketed for bulk unsolicited outreach, and automates message sending inside web.whatsapp.com without user confirmation.
 Chrome Web Store Spam and Abuse policy, which the clone cluster violates by publishing duplicate experiences and by enabling spam and automated messaging on a user’s behalf.
Chrome Web Store Spam and Abuse policy, which the clone cluster violates by publishing duplicate experiences and by enabling spam and automated messaging on a user’s behalf.
WhatsApp Business Policy in Context
WhatsApp’s Business Messaging policy requires explicit opt-in before a business contacts a person, places the burden of proving that opt-in on the sender, and mandates fast honoring of block and opt-out requests. It also instructs businesses not to deceive, mislead, or spam and to comply with applicable laws. The extensions in this cluster are marketed for bulk outreach and ban evasion, not consent-driven conversations.
 WhatsApp Business Messaging policy requires opt-in and forbids spam or surprise messaging.
WhatsApp Business Messaging policy requires opt-in and forbids spam or surprise messaging.
Contrary to WhatsApp’s Business Messaging policy, the operators publish tutorials that teach circumvention rather than consent-based use. In a YouTube video by DBX Tecnologia, the author describes how to avoid bans by shaping traffic, for example tuning send intervals, pauses, and batch sizes, and by using templates that vary message text to reduce detection.
The goal is to keep bulk campaigns running while evading anti-spam systems. This marketing aligns with what we verified in code: document-start injection into WhatsApp Web, use of window.WPP.* helpers for message dispatch, and scheduled send logic via a Manifest V3 service worker. Together, the video and extension UI corroborate our assessment that the product is built to automate bulk messaging and to tune sending patterns in ways that aim to avoid WhatsApp anti-spam enforcement.
 In a YouTube tutorial, the author demonstrates the extension’s bulk-send screen, showing controls for send intervals, pauses, and batch size, and explicitly explains how to use it to bypass WhatsApp’s anti-spam algorithms.
In a YouTube tutorial, the author demonstrates the extension’s bulk-send screen, showing controls for send intervals, pauses, and batch size, and explicitly explains how to use it to bypass WhatsApp’s anti-spam algorithms.
Outlook and Recommendations
This campaign demonstrates policy abuse at scale that looks and behaves like a software supply chain, a single codebase cloned, lightly rebranded, and resold through affiliates. The commercial wrapper, storefronts, social channels, and tutorials, normalizes spamming that violates Chrome Web Store and WhatsApp rules. The result is wide reach, continuous re-uploads, and durability against takedowns.
Socket can turn these findings into detection and control. Use Socket’s Chrome extension protection to inventory every extension in use, surface permissions and host access, and block risky updates before they land on endpoints. The same analysis engine that flags supply chain risk in open source packages now scans hundreds of thousands of extensions and alerts on behaviors such as excessive permissions, unexpected page access, and data exfiltration.
Fold Socket into existing guardrails. Enforce allowlists in Chrome Enterprise, restrict installs to approved extension IDs, and track permission creep over time. Pair Socket’s visibility with network policy for egress control, then watch for lookalike domains as operators rotate infrastructure.
MITRE ATT&CK
- T1176.001 — Software Extensions: Browser Extensions
- T1204 — User Execution
- T1059.007 — Command and Scripting Interpreter: JavaScript
- T1217 — Browser Information Discovery
- T1005 — Data from Local System
Indicators of Compromise (IOCs)
Email Addresses
suporte@grupoopt.com[.]brkaio.feitosa@grupoopt.com[.]br
Chrome Extensions and Active Users
gioekliddhmaanejaaigfokghoakbaco(WaveZap CRM) — 112 usersephcniiibhpjpfpopmajlmbbijfjpdde(WaCelery) — users not shownfbkpechbcdilkoadejmhhamidddhdehc(Top System) — 18 usersehdekncpobdjejklgpgnjgddjdnblmei(Botflow) — 35 usersmnbdaobmkdglnmiagimcniebbgebabek(Organize-C) — 5,000 usersjelgokpkjcplgcckfiaddlfaaepohfdi(FQ Sales CRM) — 30 userspmnkmmlmbnalnbgidejbcaigahodcppn(Nexus CRM) — 23 usersipaoladdllekkdokdnemkpjfllbgplek(FLEXZAP) — 71 usersgmdnikelbimgeamkdhpdblmeekpojeei(BoostChat) — 6 userslbnhlbjmibbmogaefkppniejgaadimdb(WaZap) — 104 usersgmmcjjpciafncfbggmjhglocogcaomjb(Convverso CRM) — 44 usershjlpccojkgfkamonoaoakgjjlejonefo(JuriMind CRM) — 24 userschkaiafjmlfakkibkhbfgfklfaachmnc(ZapKan) — 31 usersoohihogmmfbinbkgaiglgeabloiehlkk(Zap Vende) — 30 usersjgfaobieaananaaahonfomlibhchkndb(AngoSeller) — 13 usersjhfdppbgfmmaecdgmboadmkaoifjnfmm(Vou Falar) — 4 usersphamkmfigepogfnbkelfmknehfcjjklm(Chatty Seller) — 23 usersjheebhheaomejiiilhgkambdgagmhfhe(GFlow Chat) — 33 usersfoedfcdeffihcmjibkbaffddbjdmkphi(CNW ZAP) — 25 usersjhiknfikchccfkhjbfgiolgjofbnmgkd(66seller) — users not showncbhhipokgmechdbhebbalpckddlnfggm(Doris CRM) — 19 userscjdcglineikacjboikmchenneanfegoo(ZappSeller) — 296 usersjmnajdcdmikociadheoaelpejbmoklpm(CliQ+) — users not shownjpfpmealiajnfjmiljnmpiifccfkaimj(À Venda - CRM) — 118 usersmcabhobmhiljmdbdigdkkhmhjieecmne(MkZap) — 19 userspedngakkndckkgfpbdmfmokokdepekho(WhatSmart CRM) — 208 userslefiaoknofkoecahieockfmhhklkigng(Sanzap) — 32 usersmcjdknfjmchailcpcolfjcogggkjfeij(WaGpro) — 112 usersmecaooaegbmnneijdhegohdpcepdbbmk(Lexchatbot) — users not shownmppgfleddoodfifpkjjjdbngnkcfcnde(performancemais) — 241 usersigmalhleeaoclfmfdlepdmfnbipkfdfi(Merlix) — 3 userseomlbgjohomgjjigponmbnedpgoegegl(ChatScript) — 6 usersmgpdpmifcljbddedpajabokdebnaemon(BC ZAP) — 44 usersofmhnbjohiadaagpeibjlncncllelaoo(Speedsflow CRM) — 5 usersofmoeicegmlaleajnpcbddiaomnfmfkp(DBX Whats) — 1,000 usershnimkbcgbhlllkcnphhhnbilkjngpphh(HGTX Intelligence Starter) — users not shownchdaaapnpinagdkdmkkoandalpdgikdh(Wabin) — 17 userscijeamgoejpplpdnjhejeeahgkbdndni(Zaplyd - CRM) — 449 userspilfkgcokfmoblofkghajplgdpmejjph(FleboLeads) — 24 userspfhinnfbeephmihjjegokhbkaeckdldp(Monchat) — 5 usershpopdnbfeddglbokfbainoglnhhoccpb(Zappower) — 29 usersgclllmamoegojkehkkohcfcjdmgikldc(Converzap) — 7 usershnnbkomgboilfohfkpfgnlcpalcnangb(Bot Imobiliário) — 50 usershocidiaogjnnibkadkedncomnglnehjg(Lucra Zap) — users not shownniimbdmbkndibiabpoolngcjipgndijh(Donna CRM) — users not shownokdhkkpmmhinmjipggbfpjbdlckkaemb(Zaplyn) — users not shownmjailbbfmgaoojmjfcacffkdjoccggcf(FácilCRM) — 174 usersaippcgffdfgfkihejnjkmkbjoidpemcl(IV-CHAT) — users not shownbajadmkhmpjaiibgakhdgpgllgnhdocc(Talk Zap CRM) — 33 usersbmcliihacfhpicjacebpnhliojphelck(Sellerwork) — 15 usersmjhdkfgdfcehianhcmjpgpicelgehbbe(Wazapy) — 4 usersmhcnngbhhpmlahekicpkpammjibamlip(SALES WHATS) — 213 usersjfcekpbabbijmfpcgnnoaekodnagbffd(Super Chat Boom) — users not shownahpcdagejgoffjpnbkhemojogbocbahe(ChatAds) — 122 usersmkbjflhgpickfellipdmpcnhkmmdcojl(YouSeller) — 10,000 usersnmnflpdnbpnoojmpmhkkiagmegimlnmm(FLOW 5.0) — users not shownnnmbiaaomdknpkgpklfcekneilkimoal(TELEFON CONECTA) — 13 usersbjbdjeijmkjcphbmbiifoeaikbmmgcjp(WA FLASH) — 104 userskekglidebofmckpkojgbogajflnmhega(MovvaSe) — users not shownkfopgoafhfkcpnkiemaldlplpbnengjf(Power Chat) — 25 usersnmimioepofbhnidpmebigbahpckjfmbm(Chatfunel) — 54 usersclpedhieolcgejlfdnlfadojpaiahlfm(VicChat) — users not shownpmdahofhcbcejdodnmijkhahahegenhi(INWISE CRM) — 13 usershhlbnnfmjdoeegpoihgandmppnmfpeib(ZapForce) — 8 usersjleilnojaafdekbbpighcjlcbmfnifim(ZapWild - CRM) — users not shownmaopdiomoidladgapokmfggnccpolbol(WhatsTool) — 27 userscgcckeanlanlpaflhipplbhichjejgpk(Lever CRM) — 81 userskleicpolamoebhoajpbhcbmcihbcfobm(Opendoor Solucoes) — users not shownkmhlbkgpafhoojblcfhnljaaighbejfk(Yconecta Latam) — 9 usersifhkkkfghpgbelajdcmkbahibfieffkl(Pipe Loom) — users not shownblpopmcoebhlkolmkjjmplbmlgdhggkk(Connect Castle Solution) — users not shownbegphlgbbimlphmfbigfjcadjgplglcg(ATENDO DO ZAP) — 34 usersbmeleciepnphilegegcbfjkoolldigid(SYS.AO) — 23 usersebmbbmldkfhfambpnegomegconmhcioe(Evoluwa) — users not shownddmhkpkipjnhlppmcepckfgjbmljmphm(Maiq) — 7 usersjjopcmgbpnfdehgmbioibahegdmmfipm(Zap4u) — users not shownhdonddbodcfamjgmdolkgfgidjfmijmj(Evan’s Atende) — 33 usersanoghcdepimhncglcecmgnbchpjfkonp(MestreZap) — users not shownoiekdjliebhjpjknfojajhjebgeedhag(Salesly) — 7 usersohekppieeepibkebnlilabljmnkffmof(ZapLead) — 25 usersohojiglgbgnhaddfhdbkoclekhghncih(Chat Power) — users not shownekigeoglcndojhecmojcchlhjkbghnmg(FarChat) — 28 usersmlladklbipjfnjgjjbkofonboojklnpo(idk Converte) — 6 usersedgokehfaihammibdolojeljlccobihi(VEXA INOVAÇÃO) — 2 userseecbjpnghjlfeanpabnebopncfldgkej(Polo Lucrativo) — 6 usersnamibohbbclnmgbnhegongpbkphhelji(Sell Swift) — 5 usersndilbmjmeggijafdloohkniglleeekff(Red Chat) — 12 usersbpinnifebepjjedmficfllcnalhcfgin(Hizi Chat) — users not shownfkcbkncgbolfiijohpipeobfbopidhlg(HBS CONNECT) — users not shownbcabbcjlfhhffnjjfebenghlgfpfobdg(EAI MAIS) — users not shownnfoenldfhfooabacoilpappaoggfmdio(ifteczap CRM) — users not shownbmfeoaglddjefdcdmnaohgjlanmmddog(ByteZap) — 21 usersmpcajkogkmebocmcflglhmdekfglallb(Cresça & Apareça CRM) — 4 usersghlcmioojimlkcljjjepehacmgodjfdk(WHATSATLANTIC) — 87 userspoemcanhdcddpkjmdgegfiopikiheppd(Alô IA) — 6 userspmpcobjbffgoalkbilglngiomdbpmffd(ZapyPrime) — 16 userslpbhcehpljligfjkcjpfklackjfoomao(WhizzChat) — 28 userslmoncmhkblbcbekgefgpkohplhjkfgbm(RoboZapp) — 68 userscbgbkbafakhpmmdmbaafniijhifoikei(ARX Tecnologia) — 2 usersodlgfgmgiinbkobmfhgmphbpfpmofppf(Tryno CRM) — 23 usersaekhfllepcmekghgdhgbceojklhhioba(Zaptree) — 8 usersilahhiccjmanljjhebdpoilbfhjgpckp(360° Management CRM) — 22 usersagmdligmnfaciogcnokodiaoppflebla(Biz Sale Chat & CRM) — users not shownahejniinncebcikkjhggpghpjlkgjoab(Wavenda) — 44 userskajbnhbibimhcmkpeokmgdpnhddjncka(GMD-ON) — 20 userskahaenfigldjkcjpnblmhbbkkgfjkhhl(ZapCORR Suite) — 12 usersgfkedhmelaeoklidjhdbgpbnjdcacced(Zap Gestor CRM) — 12 usersgfplcnpcmgddenkggdapkcokgnkgncfe(Myboot) — users not shownmdchifijocjccoidjcaamcebbehehlgo(Sales Whats Brasil) — 7 usersebjpepgmlmbfgjdefdhobjfnhpgepibd(IMPAR CRM) — 4 usersfkkjcbogndlaeofafjjdlckkodpnlafb(Oh Mago CRM para Whatsapp) — users not showncdjijomcoohechfbkipcibpcakldfceo(DataZap: Automação, CRM) — 30 usersegebdiofdkgfhheopdaecggogdeaaepj(TekZap Conversas) — 46 usersnhmcfloglkbnliknncnfnlhideepfpfi(Lobo Vendedor) — users not shownfdofhoefhcjllmgcgpdplndaeebfnica(Gana Digital) — users not showniflolbkfpmpjobjhkamajiekpmepcban(WHATZIP) — 19 usersdcgdocmggapfdocodbimagkloacnkbjf(STUDIO ZAP) — 37 usersllijmcnalgidmchdckmpimhhffehfbbg(Novo Envio Extensão: CRM) — 110 userseaeiigegpmgegjhcbohmhddjgaldbknn(FortChat) — users not shownfibommgfjfckaingpopkdohoegidkmng(Cash Zapp) — 17 usersfgfbklebnaaimlcgmfohnlnkihahlagk(ChatBlink) — 786 userscjiedabijhhefgeonkdodnpaiimfdlpd(Projeta Zap) — 49 userslhngnpihljickmbkflaiobcblmhchpab(Conectadus CRM) — 13 usersjpioocoiojejijkbnpljcoonohmechha(Zap4Biz) — users not shownhaieolmfmmepgdimacfanclfemodnmep(BYS Convert) — users not shownfjfpgmaghnjnjndiapfmehebankomkmc(Fluxo de Vendas) — 10 usersclkibjppajhlbhofckbilehgfjjmljnj(Evento Prime) — users not shownjbkmdabbenlckohhpccihkingphnoaom(WizeChat) — users not shownoikahlogkilifeoehlepbljmnjohannb(MyZapCRM) — 1 useraogcmjgadbnlpjjcppfcjndmnffbeiid(Vozco Scale) — 10 usersdknafkoneldddpgcomhckilhhfodcnkk(Atendi Light) — users not shown
Marketing Websites
organize-c[.]com— Organize-Czapvende[.]com— Zap Vendechattyseller[.]com— Chatty Sellerzappseller[.]com[.]br— ZappSellermkzap[.]com[.]br— MkZapwww[.]bcmarketing[.]com[.]br/lp— BC ZAPdbx[.]global/whats/— DBX Whatszappower[.]com[.]br— Zappowerlucrazap[.]com[.]br— Lucra Zapfacilcrm[.]com[.]br— FácilCRMyouseller[.]com[.]br— YouSellerpowerchat[.]in— Power Chatchatfunnel[.]com[.]br— Chatfunelzapforce[.]app[.]br— ZapForcewhatstool[.]in— WhatsToolcuriosidademinha[.]com[.]br/atendodozap— ATENDO DO ZAPzap4u[.]com[.]br— Zap4umestrezap[.]online— MestreZapchatpowerpro[.]com[.]br— Chat Powerchat[.]bizsale[.]com[.]br— Biz Sale Chat & CRMlobovendedor[.]com[.]br— Lobo Vendedorganadigital[.]com[.]br— Gana Digitalwizechat[.]com[.]br— WizeChat